EdDSA – Understanding the Digital Signature Algorithm
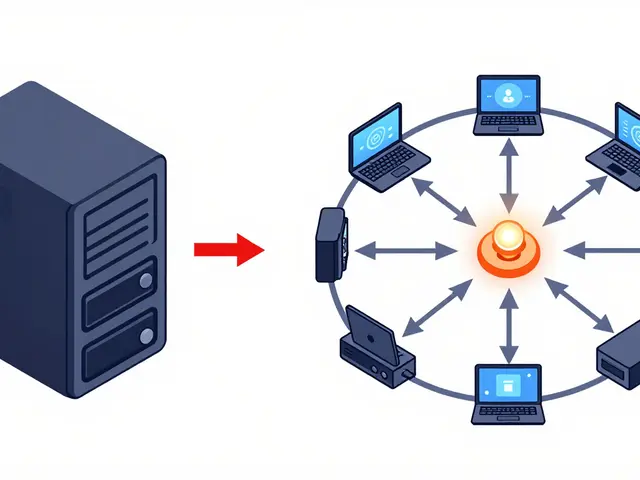
When working with EdDSA, the Edwards‑curve Digital Signature Algorithm, a modern signing scheme that delivers fast, provably secure signatures. Also known as Edwards‑curve DSA, it builds on Elliptic Curve Cryptography, a set of techniques that use the mathematics of elliptic curves to generate public‑key pairs and depends on cryptographic hash functions, algorithms that compress data into fixed‑size digests for integrity verification. In any blockchain, digital signatures, cryptographic proofs that a transaction originated from the holder of a private key are the backbone of trust. That’s why developers choose EdDSA for wallets, smart contracts, and cross‑chain bridges – it offers strong security with tiny signatures and low verification cost. In short, EdDSA provides robust protection without slowing down the network.
Why EdDSA matters for crypto projects and everyday users
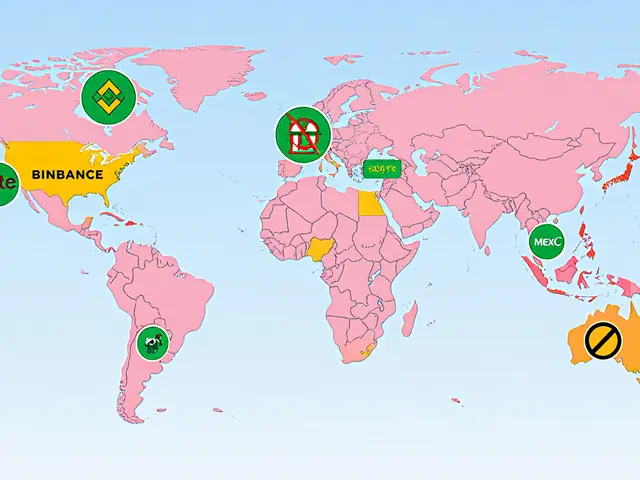
Think about a typical crypto exchange that needs to authenticate API calls, airdrop claim processes that must prove eligibility, or a DeFi platform that signs off‑chain messages. All these actions rely on digital signatures, the same cryptographic primitive that EdDSA implements. By using EdDSA, exchanges can reduce latency in trade confirmations, airdrop bots can verify participants with a single lightweight proof, and wallet apps can keep private keys safe while still proving ownership instantly. The algorithm’s resistance to side‑channel attacks also aligns with the security best practices discussed in our guides on NFT marketplace safety and blockchain energy data management. Whether you’re tracking a new token listing, reading a review of 6x.com exchange, or checking the latest regulation updates for India or Taiwan, the underlying trust model often starts with a solid signature scheme like EdDSA.
Below you’ll find a curated set of articles that dive deep into the crypto ecosystem – from airdrop mechanics and exchange reviews to regulatory analyses and blockchain fundamentals. Each piece shows how the concepts around digital signatures, elliptic‑curve math, and hash‑based security play out in real‑world projects. Browse the list to see how EdDSA‑compatible designs power the tools you rely on, and pick up practical tips to keep your assets safe while staying ahead of market moves.
Explore the main digital signature algorithms behind blockchain-ECDSA, EdDSA, Schnorr and more. Learn how they work, compare security, performance, and future quantum‑ready options.



 Finance
Finance