Imagine a heist where the thieves don't break down doors or crack safes. Instead, they send a fake job application via LinkedIn, wait months for the right moment, and then quietly drain billions from digital wallets while everyone else is sleeping. This isn't a movie plot; it's the reality of state-sponsored cybercrime. Between 2017 and 2023, North Korean hackers stole approximately $3 billion in cryptocurrency, according to United Nations Security Council assessments reported in late 2024. But that number is now outdated. In early 2025 alone, a single attack on the Dubai-based exchange Bybit resulted in nearly $1.5 billion stolen, marking the largest cryptocurrency theft in history.
If you're holding digital assets or working in the fintech space, understanding this threat isn't just about curiosity-it's about survival. These aren't random criminals looking for quick cash. They are sophisticated, state-funded operations designed to circumvent international sanctions and fund weapons programs. To protect yourself or your organization, you need to understand who they are, how they operate, and what restrictions are currently being implemented to stop them.
The Scale of the Theft: From $3 Billion to Record Highs
To grasp the magnitude of this issue, we have to look at the numbers. For years, experts tracked North Korean cyber activities as a growing concern. Between 2017 and 2023, these groups executed 58 separate cyberattacks, stealing roughly $3 billion. That sounds like a lot, but the pace has accelerated dramatically. In 2024, North Korean-affiliated groups stole $1.34 billion across 47 incidents. This represented a massive 102% increase from the $660 million stolen in 2023.
Why the spike? As traditional revenue sources dried up due to tightening global sanctions, Pyongyang turned more aggressively to the digital economy. In 2024, these groups accounted for 61% of all cryptocurrency stolen globally, despite representing only 20% of total cyber incidents. This indicates a higher success rate and superior targeting compared to other threat actors. Then came February 2025. The Bybit hack shattered previous records. Nearly $1.5 billion worth of Ether was stolen in one go. This single event exceeded the combined value of all 47 hacks throughout 2024. It showed that the ceiling for these attacks doesn't exist-they will keep scaling up until stopped.
Who Are the Hackers Behind the Heists?
When people talk about "North Korean hackers," they aren't talking about a single person in a basement. They are referring to several highly organized, state-sponsored units. Each group has its own specialty, but they all report back to the same goal: generating hard currency for the regime. Here are the primary entities you need to know:
- Lazarus Group: The most famous of the bunch. Active since the early 2010s, Lazarus is known for high-profile attacks on banks and crypto exchanges. They set the standard for state-sponsored crypto theft.
- TraderTraitor: A newer, highly agile group focused specifically on cryptocurrency infrastructure. They were responsible for major hacks in 2023, including attacks on Atomic Wallet and CoinsPaid.
- Jade Sleet: Known for their social engineering prowess. They excel at infiltrating companies by posing as recruiters or partners.
- UNC4899: A unit often linked to supply chain attacks, compromising software vendors to reach downstream victims.
- Slow Pisces: Another emerging group identified in recent UN reports, contributing to the overall volume of thefts.
These groups don't work in isolation. Intelligence sharing between the FBI, the Department of Defense Cyber Crime Center, and international partners like Japan's National Police Agency helps map their connections. However, attribution remains complex. Chainalysis, a leading blockchain intelligence firm, has noted that some large hacks previously attributed to North Korea were later found to be unrelated, while smaller incidents were newly identified as DPRK-linked. This constant re-evaluation shows how fluid and deceptive these operations are.
The Anatomy of an Attack: How They Steal Billions
You might wonder how anyone can steal $300 million or $1.5 billion without triggering alarms immediately. The secret lies in patience and social engineering. Let's look at two major cases to understand the methodology.
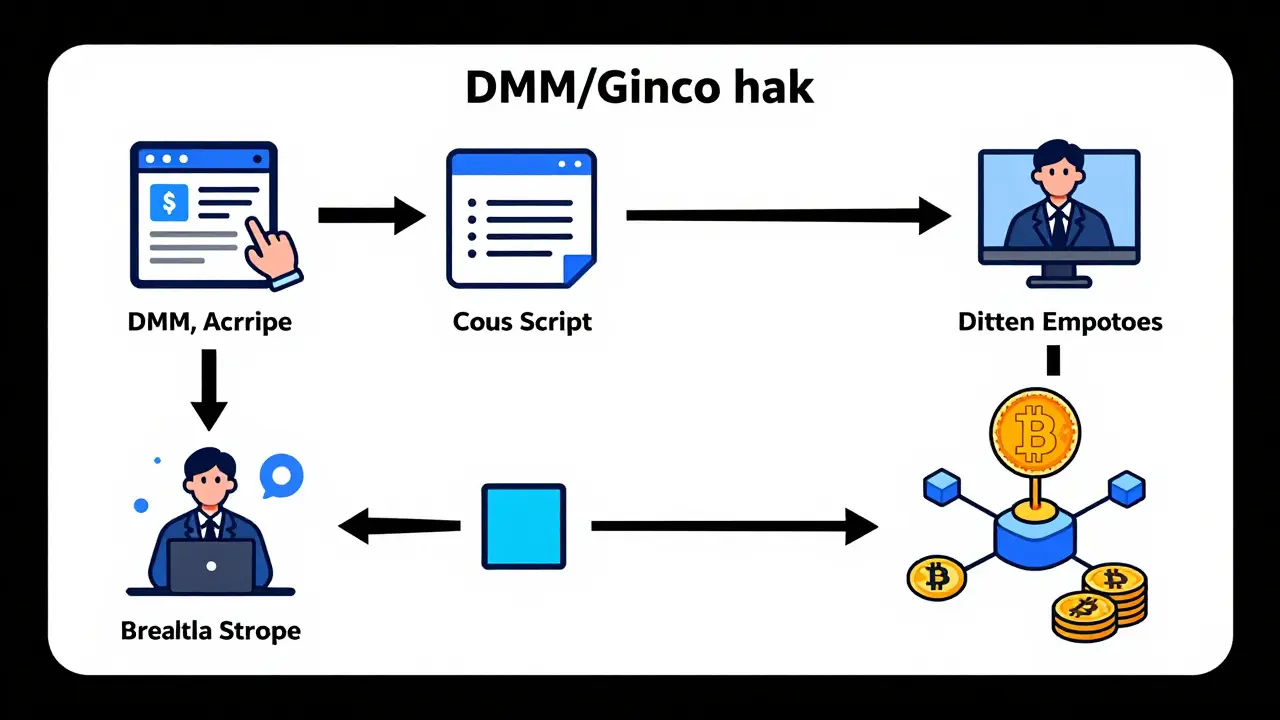
The DMM/Ginco Incident (2024)
In May 2024, Japanese platform DMM lost $308 million. The attack didn't start with a code exploit. It started on LinkedIn. North Korean actors, likely from the Jade Sleet or UNC4899 groups, posed as recruiters. They targeted employees at Ginco, a company that provides wallet software for DMM. The victims received a malicious Python script disguised as a pre-employment test hosted on GitHub. Once an employee ran the script, their machine was compromised. The attackers then harvested session cookies, allowing them to impersonate the employee and access unencrypted communication systems. Months later, they manipulated a legitimate transaction request, sending 4,502 BTC to their own wallets. The entire operation took months because they needed to build trust and understand internal processes.
The Bybit Heist (2025)
The February 2025 Bybit attack was different in scale but similar in sophistication. Hackers stole nearly $1.5 billion in Ether. Unlike the DMM case which relied heavily on human error, this attack likely involved deeper technical exploits within the exchange's hot wallets or bridge protocols. After the theft, the hackers moved quickly. TRM Labs analysis showed they rapidly converted the stolen Ether into Bitcoin and other digital currencies using decentralized exchanges (DEXs) and cross-chain bridges. This laundering process dispersed funds across thousands of virtual wallets, making it incredibly difficult for law enforcement to trace the money back to its source.
Why Cryptocurrency? The Sanctions Evasion Strategy
Why does North Korea care so much about crypto? The answer is simple: sanctions. Traditional banking channels are largely closed to the DPRK. They cannot easily move money through SWIFT or hold accounts in Western banks. Cryptocurrency offers anonymity, borderless transfers, and instant settlement. For the North Korean regime, crypto isn't just investment; it's a lifeline. U.S. and international officials assess that these funds directly finance weapons of mass destruction and ballistic missile programs. Every dollar stolen is a dollar that could buy materials for nuclear development. This makes these attacks not just financial crimes, but national security threats.

Restrictions and Countermeasures: What Is Being Done?
Given the scale of the threat, governments and the private sector are implementing stricter restrictions. If you are operating in the crypto space, you need to be aware of these changes.
- Enhanced KYC/AML Rules: Exchanges are under pressure to implement stricter Know Your Customer (KYC) and Anti-Money Laundering (AML) protocols. This includes real-time monitoring of transactions linked to known North Korean wallet addresses.
- Travel Rule Compliance: Regulations requiring exchanges to share sender and receiver information for transfers above certain thresholds are being enforced more rigorously to disrupt the anonymization tactics used by hackers.
- Freezing Assets: Governments, particularly the U.S. Treasury's Office of Foreign Assets Control (OFAC), regularly publish lists of sanctioned wallet addresses. Any interaction with these addresses can result in severe penalties for businesses.
- Multi-Signature Mandates: Industry best practices now strongly mandate multi-signature wallets for corporate treasuries. No single employee should have the ability to move large sums of capital.
- Employee Training Programs: Following the DMM incident, there is a renewed focus on training staff to recognize social engineering attempts, particularly those coming from professional networking sites like LinkedIn.
| Date | Target | Amount Stolen | Primary Tactic |
|---|---|---|---|
| Feb 2025 | Bybit | ~$1.5 Billion | Technical Exploit & Rapid Laundering |
| May 2024 | DMM / Ginco | $308 Million | Social Engineering (LinkedIn Recruitment) |
| June 2023 | Atomic Wallet | $100 Million | Supply Chain Compromise |
| June 2023 | Alphapo | $60 Million | Direct Platform Exploit |
Protecting Yourself and Your Business
So, what can you do? If you are an individual investor, the risk is lower, but not zero. Never share your private keys. Use hardware wallets for long-term storage. Be wary of unsolicited messages on professional networks. If you run a business or work in tech, the stakes are higher. Implement strict access controls. Assume that any external link or file is potentially malicious. Conduct regular security audits. Most importantly, educate your team. The weakest link in any security chain is often human error. North Korean hackers are patient; they will wait for the right moment to strike. Don't give them the opportunity.
How much has North Korea stolen in cryptocurrency since 2017?
Between 2017 and 2023, North Korean hackers stole approximately $3 billion across 58 incidents. However, this number has grown significantly. In 2024 alone, they stole $1.34 billion, and in February 2025, a single attack on Bybit resulted in nearly $1.5 billion stolen. Total losses now exceed $5 billion when including the 2025 incidents.
Who are the main North Korean hacker groups?
The primary groups include Lazarus Group, TraderTraitor, Jade Sleet, UNC4899, and Slow Pisces. These are state-sponsored units that specialize in different aspects of cyberattacks, from social engineering to technical exploits.
What was the Bybit hack in 2025?
The Bybit hack, occurring in February 2025, is the largest cryptocurrency theft in history. Hackers stole nearly $1.5 billion worth of Ether. The attackers rapidly converted the assets into Bitcoin and other currencies using decentralized exchanges to obscure the trail.
How did North Korean hackers steal from DMM in 2024?
They used social engineering. Posing as recruiters on LinkedIn, they sent malicious Python scripts disguised as job tests to employees at Ginco, DMM's wallet provider. After compromising an employee's system, they hijacked sessions and manipulated a legitimate transaction to steal $308 million.
Why does North Korea target cryptocurrency?
Cryptocurrency allows North Korea to circumvent international sanctions. Since traditional banking channels are closed to them, crypto provides a way to generate hard currency to fund weapons of mass destruction and ballistic missile programs.
What restrictions are being put in place to stop these hacks?
Restrictions include enhanced KYC/AML rules, stricter Travel Rule compliance, freezing of sanctioned wallet addresses, mandates for multi-signature wallets, and improved employee training against social engineering.
Is my personal crypto wallet safe from North Korean hackers?
While less likely than exchange hacks, individual users are still targets if they fall for phishing scams or social engineering. Using hardware wallets, enabling two-factor authentication, and never sharing private keys significantly reduces risk.
Which countries are leading the fight against North Korean crypto theft?
The United States (via the FBI and OFAC), Japan (National Police Agency), and international bodies like the UN Security Council are leading efforts. Blockchain analytics firms like Chainalysis and TRM Labs also play a crucial role in tracking funds.



 Finance
Finance




