On February 21, 2025, the cryptocurrency world woke up to a nightmare scenario. ByBit, one of the largest digital asset exchanges globally, had been breached. The attackers didn’t just take a few wallets; they stole approximately $1.5 billion worth of Ethereum tokens. This wasn't a random hacker in a basement. It was a state-sponsored operation by North Korea, marking the single largest cryptocurrency heist in history.
This event changed everything we thought we knew about exchange security. For years, we believed that if funds were stored in offline "cold storage," they were safe. That assumption is now dead. Understanding how this happened, who did it, and what it means for your assets is crucial for anyone involved in the crypto ecosystem today.
The Perpetrators: Who Is TraderTraitor?
The Federal Bureau of Investigation (FBI) didn't guess who pulled this off. They officially attributed the attack to a specific subunit known as TraderTraitor. This group operates under the 3rd Bureau of the Democratic People’s Republic of Korea’s (DPRK) Reconnaissance General Bureau (RGB). If you’ve heard of the Lazarus Group, think of TraderTraitor as its specialized financial division.
TraderTraitor has been active since at least 2022. Unlike earlier North Korean cyber units that relied on simple phishing emails or basic malware, this group focuses exclusively on stealing digital assets through sophisticated technical exploits. They are not interested in data leaks or espionage; they want money. Specifically, they want hard currency to fund the DPRK’s weapons programs.
In 2024, North Korea stole about $800 million across 47 separate incidents. The ByBit hack alone nearly doubled that entire year’s total. This shows a strategic shift from many small attacks to fewer, massive strikes. The FBI designated this specific campaign as "TraderTraitor" to distinguish it from other North Korean activities, signaling that this is a distinct, high-priority threat actor.
How the Attack Worked: Breaking the Cold Wallet
The most shocking part of the ByBit breach wasn't the amount stolen-it was how easy it seemed to be once the door was open. The hackers compromised one of ByBit’s offline cold wallets. In the crypto world, a cold wallet is supposed to be air-gapped, meaning it’s never connected to the internet. It’s the vault within the vault.
Blockchain analytics firm TRM Labs determined with high confidence that the breach resulted from one of three scenarios:
- A supply chain compromise where malicious code entered via a trusted software update. >An insider threat where an employee or contractor leaked credentials.
- A sophisticated private key compromise that bypassed multi-signature security measures.
Whichever method was used, the result was the same: the attackers gained unauthorized access to private keys. They then moved the stolen Ethereum rapidly. Speed is their best friend. Within hours, portions of the stolen funds were converted through various blockchain networks, including Binance Smart Chain and Solana, before being settled into Bitcoin.
The Laundering Strategy: Flood the Zone
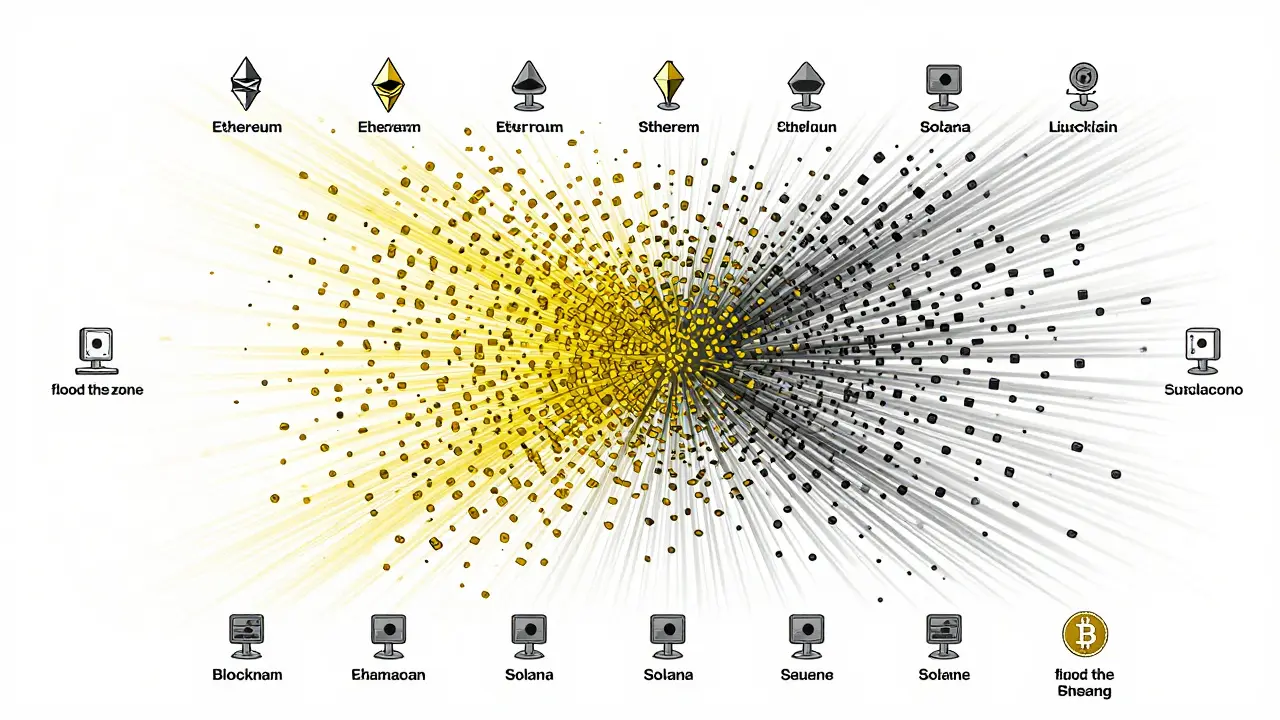
Once the money was out, the real challenge began: hiding it. In the past, North Korean hackers relied heavily on mixing services like Tornado Cash to obscure transaction trails. But regulators have cracked down on these mixers. So, TraderTraitor evolved.
Nick Carlsen, a former FBI subject matter expert and North Korea specialist at TRM Labs, calls this new approach "flood the zone." Instead of trying to hide behind anonymity tools, the hackers overwhelm compliance teams and blockchain analysts with sheer volume and speed. They distributed the stolen assets across thousands of addresses on multiple blockchains simultaneously.
This strategy makes manual tracking nearly impossible. Automated systems struggle to keep up when transactions happen in milliseconds across different chains. Most of the converted Bitcoin remained stationary after the initial laundering phase. This suggests the hackers aren't trying to spend it immediately but are preparing for large-scale liquidation through over-the-counter (OTC) networks, where they can sell bulk amounts without triggering standard exchange alerts.
Why Exchanges Are Prime Targets
You might wonder why North Korea targets crypto exchanges instead of traditional banks. The answer lies in risk versus reward. Traditional financial institutions have decades-old security infrastructure, strict regulatory oversight, and immediate law enforcement response protocols. Crypto exchanges, while improving, often operate in a regulatory gray area with varying levels of security maturity.
Furthermore, the payout is instant and borderless. A bank transfer can be frozen mid-flight. A blockchain transaction, once confirmed, is irreversible. For a regime under heavy sanctions, crypto offers a direct line to usable foreign currency. A United Nations report noted that approximately 50% of North Korea’s foreign-currency earnings come from cybercrime. This $1.5 billion heist isn't just a crime; it's a national security issue for the entire globe.
| Tactic | Traditional Approach (Pre-2022) | TraderTraitor Approach (2025+) |
|---|---|---|
| Primary Vector | Phishing & Basic Malware | Supply Chain Compromises & Private Key Exploits |
| Laundering Method | Mixers (Tornado Cash, Sinbad) | Cross-Chain Bridges & High-Frequency Transactions |
| Target Profile | Individual Users & Small DeFi Protocols | Major Centralized Exchanges (CEXs) |
| Speed of Execution | Days to Weeks | Hours to Minutes |
| Detection Difficulty | Moderate (Traceable clusters) | High (Overwhelms analysis tools) |
The Industry Response: Blocking the Flow
The reaction to the ByBit hack was unusually fast. The FBI released specific Ethereum addresses associated with TraderTraitor actors almost immediately. They didn't just ask police to investigate; they asked the tech industry to act. RPC node operators, exchanges, bridges, and blockchain analytics firms were urged to block transactions from these addresses.
This highlights a new reality in cybersecurity: public-private cooperation is no longer optional. Law enforcement cannot stop a blockchain transaction on their own. They need the infrastructure providers-like ByBit, Coinbase, or Binance-to refuse to process or accept funds from flagged wallets. TRM Labs created a tracking entity labeled "Bybit Exploiter Feb 2025" to help these companies monitor real-time movements.
However, this creates a cat-and-mouse game. As soon as one address is blocked, the hackers move to another. The "flood the zone" tactic ensures that even if some funds are frozen, others slip through the cracks. The goal is to make the cost of blocking higher than the benefit.
What This Means for Your Security
If you hold crypto on an exchange, you need to understand the implications of this hack. The compromise of a cold wallet proves that no system is immune to state-level actors. Multi-signature wallets, which require multiple keys to authorize a transaction, were bypassed. This suggests that the vulnerability wasn't just technical but potentially procedural or human.
For individual users, the lesson is clear: not your keys, not your coins. While exchanges offer convenience, they also present a centralized target. If you are holding significant amounts, consider using a hardware wallet that you control entirely. Even then, stay vigilant. Supply chain attacks can affect hardware manufacturers too. Always download firmware updates directly from official sources and verify checksums.
For developers and businesses, this incident signals a need to reassess security assumptions. Auditing smart contracts is no longer enough. You must audit your entire supply chain, including third-party libraries, cloud service configurations, and employee access rights. Insider threats remain one of the hardest vectors to defend against because they start from inside the perimeter.
Future Outlook: Escalation Is Likely
The success of the ByBit hack will likely encourage further escalation. North Korea has proven that it can execute complex, high-value heists with relative impunity. The $1.5 billion haul exceeds their entire 2023 crypto theft total of $660.5 million. This demonstrates increasing capability and ambition.
We may see more attacks on centralized exchanges, particularly those with weaker regulatory oversight or less mature security teams. We may also see increased focus on cross-chain bridges, which are notoriously vulnerable due to their complexity. The intersection of cybersecurity, national security, and finance is blurring. What was once considered a niche tech problem is now a global economic threat.
International cooperation will be essential. Sanctions alone won't stop TraderTraitor. We need standardized blocking lists, real-time sharing of threat intelligence between exchanges, and perhaps even regulatory frameworks that force exchanges to maintain certain security baselines. Until then, the era of big-game hunting in crypto is here, and the hunters are well-funded, highly skilled, and relentless.
Who hacked ByBit in 2025?
The hack was executed by a North Korean state-sponsored hacking unit called TraderTraitor, which operates under the Reconnaissance General Bureau's 3rd Bureau. The FBI officially attributed the attack to this group.
How much money was stolen in the ByBit hack?
Approximately $1.5 billion USD worth of Ethereum tokens were stolen. This is the largest single cryptocurrency theft in history.
Was the stolen money taken from hot or cold wallets?
The attackers compromised one of ByBit's offline cold wallets. This is significant because cold wallets are typically air-gapped and considered the most secure form of storage.
What is the "flood the zone" technique?
This is a laundering strategy where hackers move stolen funds rapidly across thousands of addresses and multiple blockchains simultaneously. This overwhelms tracking tools and compliance teams, making it difficult to freeze the assets quickly.
Is my crypto safe on exchanges after this hack?
While most exchanges remain secure, this hack shows that even top-tier security can be breached by state actors. For large holdings, experts recommend using personal hardware wallets rather than keeping funds on centralized exchanges.
How does TraderTraitor differ from the Lazarus Group?
Lazarus Group is an umbrella term for North Korean cyber operations. TraderTraitor is a specific subunit within that structure focused exclusively on financial theft via sophisticated technical exploits, rather than general espionage or simple phishing.
Why do North Korean hackers target crypto exchanges?
Crypto offers a way to generate foreign currency despite international sanctions. Exchanges are targeted because they hold large volumes of liquid assets and historically have had lower security barriers compared to traditional banking institutions.



 Finance
Finance




